Key metrics
-
10,000active clients
-
Cloud-nativebackend in Go, large AWS footprint managed with Terraform
-
1Ybuilt by a 6-person team in 12 months
About the Client
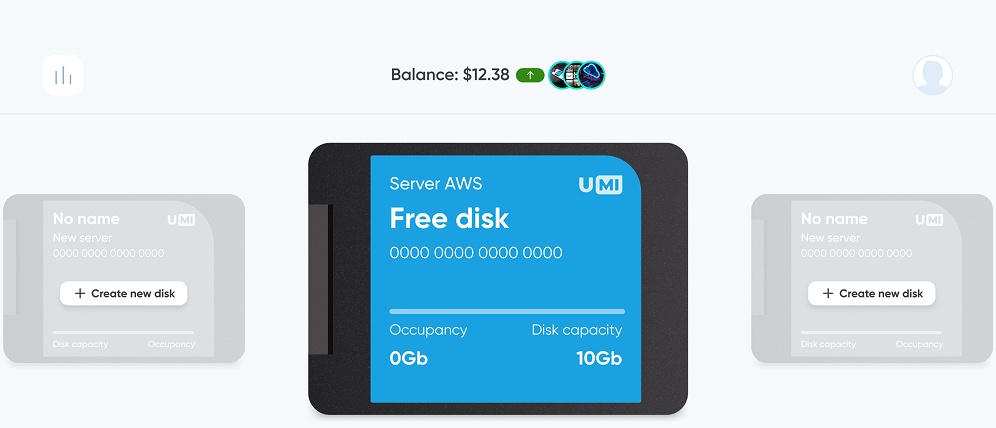
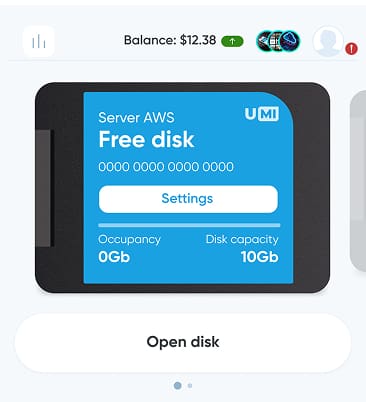
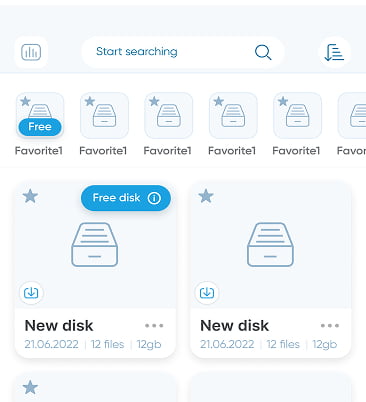
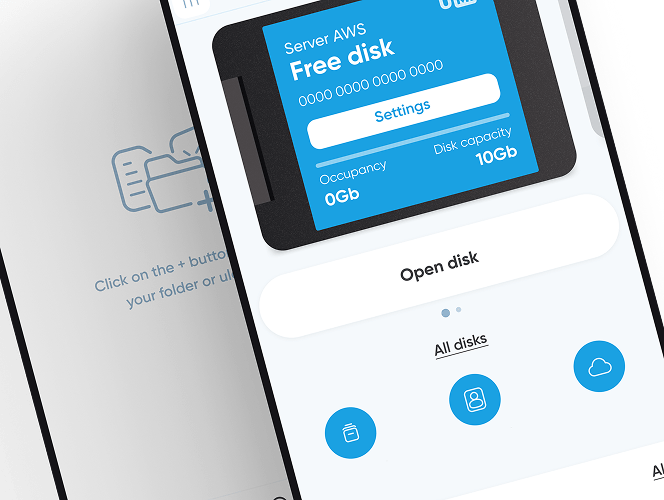
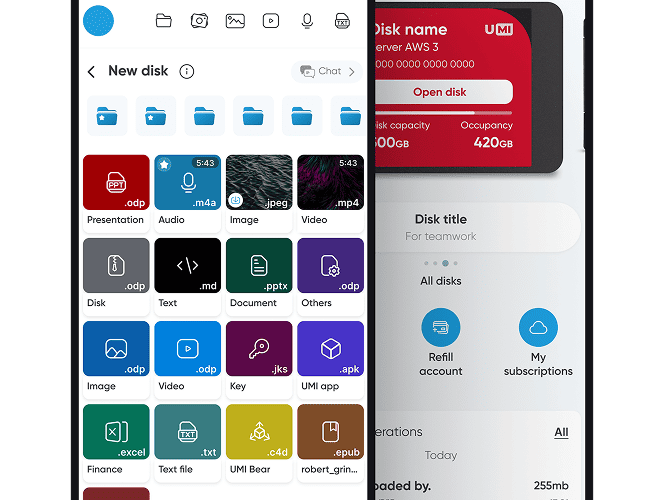
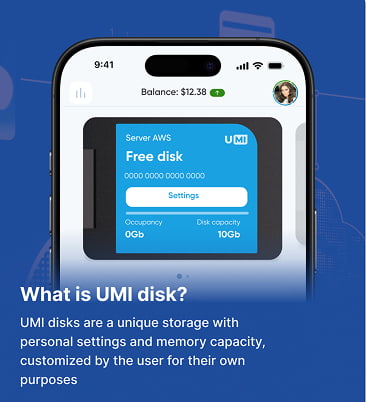
UMI is a universal platform for file storage, collaboration, and monetization. It offers virtual disks, secure sharing, role-based access, analytics, integrations, and mobile apps on iOS and Android. Files can be shared via public, secure, or paid links. The platform includes encryption and activity monitoring to protect data.
The Challenge
Create an all-in-one cloud storage product that blends secure file storage, real-time collaboration, and content monetization while remaining simple to use and ready for scale.
UMI needed to serve consumers, freelancers, and businesses from a single platform. The product vision included virtual disks, strong access control, safe and paid sharing options, subscriptions, integrations with familiar tools, and mobile access.
-
Unify many workflows in one product without sacrificing simplicity
-
Guarantee end-to-end security with encryption and granular permissions
-
Support rapid growth and heavy file operations at low latency
-
Deliver consistent experiences on web and mobile
The Solution
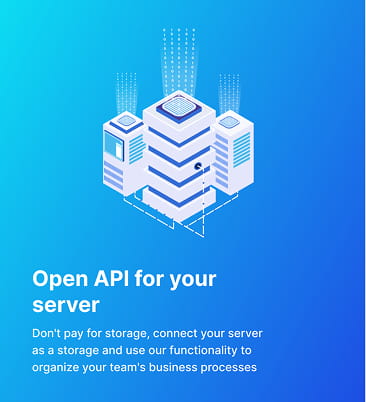
We designed a modular Go backend deployed as containerized services on AWS, fronted by application load balancers and protected by WAF.
We managed everything as code with Terraform and Terragrunt. We implemented S3-based storage tiers, Aurora PostgreSQL for relational data, DynamoDB for high-throughput tables, Cognito for auth, SQS for decoupling, and CloudWatch for observability.
Mobile and web apps consume a clean API and support secure links, role-based access, analytics, and integrations.
Go, AWS (ECS, ALB, VPC, NAT, Route 53, ACM, WAFv2, S3, DynamoDB, Aurora PostgreSQL, SES, SNS, SQS, CloudWatch, KMS, Secrets Manager), Terraform and Terragrunt, mobile apps on iOS and Android (Dart)
-
Implementation detailsPhase 1. Initial assessment and architecture
-
Requirements and domain mapping for storage, sharing, collaboration, and monetization
-
High-level service boundaries and API design
-
Landing-zone planning for multi-environment AWS with VPC, subnets, NAT, and WAF
-
-
Implementation detailsPhase 2. Infrastructure as Code
-
VPC module with public, private, database, intra, and additional subnets
-
NAT gateway strategy and security groups for ALB and services
-
Route 53 hosted zone and ACM certificates
-
ECS cluster with container insights and log KMS keys
-
Aurora PostgreSQL cluster and subnet groups
-
S3 buckets for hot, IA, Glacier, and Deep Archive with lifecycle rules
-
WAFv2 web ACL and optional IP allowlist
-
SES domain setup and DKIM, SNS SMS preferences, SQS queues, CloudWatch dashboards (derived from your Terraform modules and live folders)
-
-
Implementation detailsPhase 3. Services and features
-
Go services for archive, auth, file, payments, and thumbnail generation on ECS
-
Auth with Cognito user pool and app clients
-
Secure file links with passwords, IP limits, and expirations
-
Role-based access control and activity logs
-
Virtual disks with configurable volume and access parameters
-
Analytics, subscription monetization, and integrations with tools like Trello and CRM systems
-
-
Implementation detailsPhase 4. Security, monitoring, and performance
-
KMS for logs and sensitive configs
-
CloudWatch logs, dashboards, and alarms
-
WAF rules and least-privilege IAM roles
-
S3 policies and lifecycle optimization
-
-
Implementation detailsPhase 5. Launch and handover
-
Staging and production in eu-central-1 with repeatable Terragrunt workflows
-
Rollout of web and mobile apps with App Store and Play Store presence
-
Key outcomes
Tech Stack
-
Backend
-
Go services on AWS ECS behind ALB, exposing a clean API for web and mobile clients
-
Data layer with Aurora PostgreSQL for relational models and DynamoDB for high-throughput tables
-
Object workflows on S3 with lifecycle tiers and pre-signed URL access, plus background media processing (e.g., thumbnails)
-
Asynchronous messaging via SQS and SNS, with observability through CloudWatch logs and metrics
-
-
Frontend
-
Web application consuming the backend API with secure uploads via pre-signed S3 URLs
-
Mobile apps built with Dart for iOS and Android using the same API and auth model
-
Role-based UI for sharing, collaboration, analytics, and paid or secure links
-
Asset efficiency via HTTP cache-control and direct media delivery from S3
-
-
Infrastructure
-
AWS VPC with public, private, and database subnets, NAT strategy, and security groups
-
Networking and edge hardening with Route 53 DNS, ACM certificates, and WAFv2
-
ECS cluster provisioned with Terraform and Terragrunt; repeatable staging and production in eu-central-1
-
Platform services: SES for email, SQS and SNS for events, CloudWatch for monitoring, KMS and Secrets Manager for keys and secrets
-
-
Security
-
Identity and access via Amazon Cognito user pools with fine-grained roles and policies
-
Encryption in transit with TLS via ACM and at rest with KMS; strict S3 bucket policies and lifecycle rules
-
Application safeguards: signed links with passwords, IP limits, and expirations; least-privilege IAM; WAF rules
-
Monitoring and audit with CloudWatch dashboards and alarms plus activity logging across services
-
Key Takeaways
-
Designing for scale and security from day one unlocks faster iteration later
-
Strong access controls and encrypted workflows build user trust in a storage product
-
Operating the cloud with Terraform and Terragrunt speeds up environments and reduces risk
Modular services and Infrastructure as Code make it easy to add features like new storage tiers, additional integrations, or more regions without re-architecture
Need a secure, scalable platform like UMI?
Talk to us and we will map a path from concept to launch in a matter of months
Contact us